If you run virtual machines with a public IP address connected to the internet, attackers immediately try to run attacks against it. Brute force attacks commonly target management ports, like RDP or SSH, to gain access to a VM. If the attacker is successful, he can take control over the VM and access other resources in the environment. To address that issue it is highly recommended to reduce the ports open, especially for the management ports. However, sometimes you will need to open to ports for some of the virtual machines for management tasks. Microsoft Azure has a simple way to address this issue, called Azure JIT virtual machine (VM) access. Just in time VM access can be used to lock down inbound traffic to your Azure VMs, reducing exposure to attacks while providing easy access to connect to VMs when needed.
To find more about Just-in-time virtual machine access in Azure Security, check out the Microsoft Docs.
How does Azure Just in Time VM Access work
In the Azure Security Center, you can enable just in time VM access; this will create a Network Security Rule (NSG) to lock down inbound traffic to the Azure VM. During the initial JIT VM access configuration, you will be configuring the ports specified, which will be managed by Azure Security Center, these ports will be locked down by the Azure Security Center using an NSGs.
Configure Azure JIT VM access
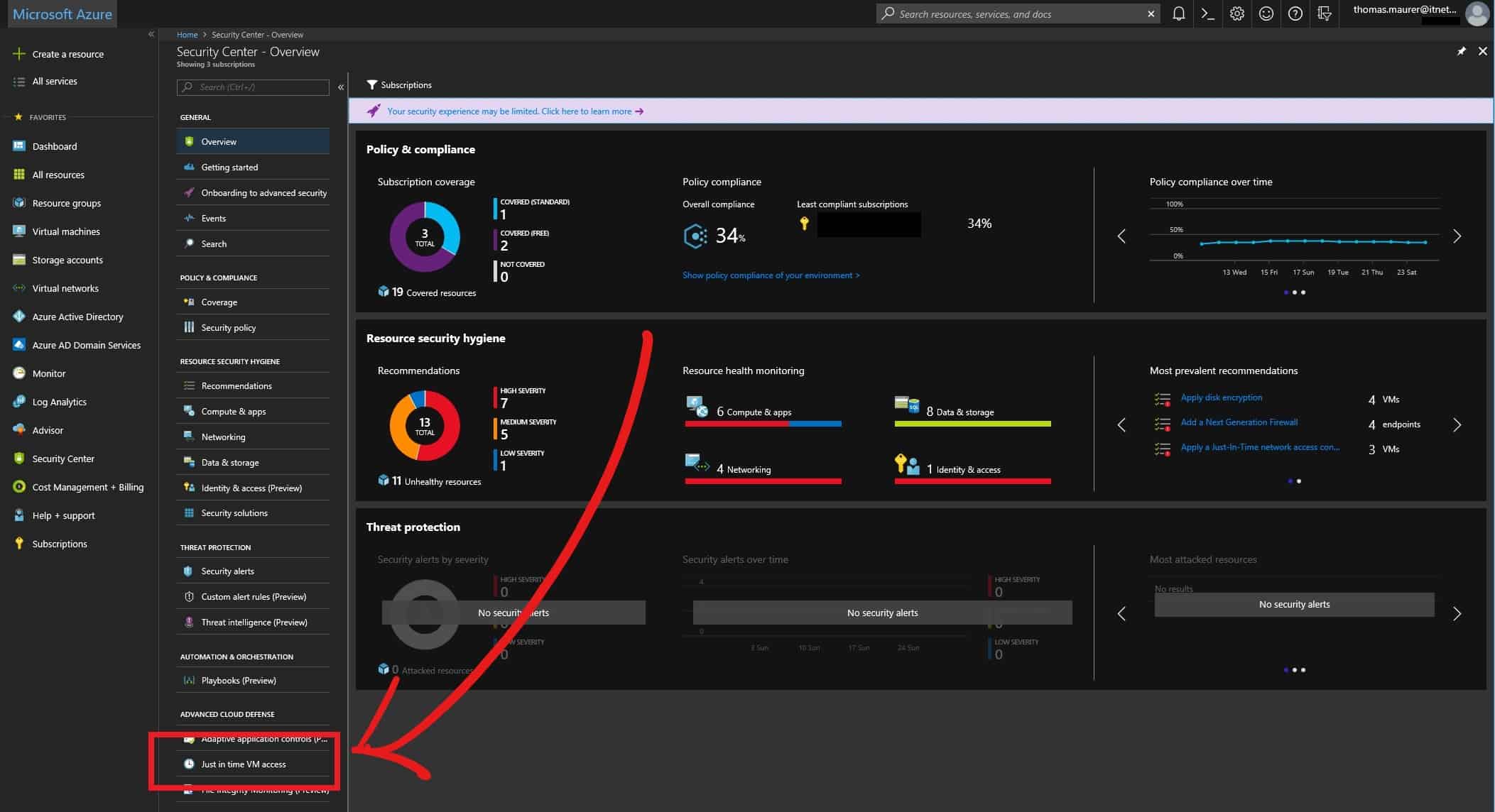
Azure JIT VM access is configured in the Azure Security Center. To configure and enable JIT on a virtual machine open up the Azure Security Center and click on Just in time VM access.
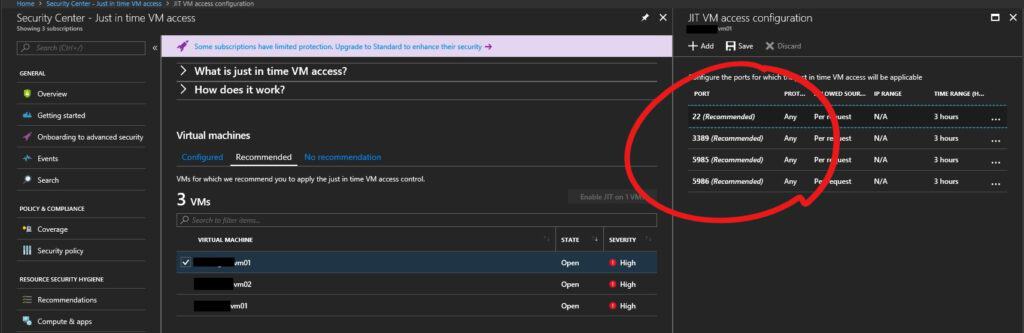
Here you will find three states, Configured, Recommended and No recommendation.
- Configured – VMs that have been set to support just in time VM access. The data presented is for the last week and includes for each VM the number of approved requests, last access date and time, and last user.
- Recommended – VMs that can support just in time VM access but have not been configured to. We recommend that you enable just in time VM access control for these VMs. See Configuring a just in time access policy.
- No recommendation – Reasons that can cause a VM not to be recommended are:
- Missing NSG – The just in time solution requires an NSG to be in place.
- Classic VM – Security Center just in time VM access currently supports only VMs deployed through Azure Resource Manager. A classic deployment is not supported by the just in time solution.
- Other – A VM is in this category if the just in time solution is turned off in the security policy of the subscription or the resource group, or that the VM is missing a public IP and doesn’t have an NSG in place.
To configure you click on Recommended and select the Virtual Machine, for which you want to enable JIT.
Click on Enable JIT on VMs and configure the ports which should be managed by Just in time VM Access. Just in time VM access will recommend some default ports like RDP, SSH, and PowerShell Remoting. You can also add other ports to the virtual machine if you want or need to.
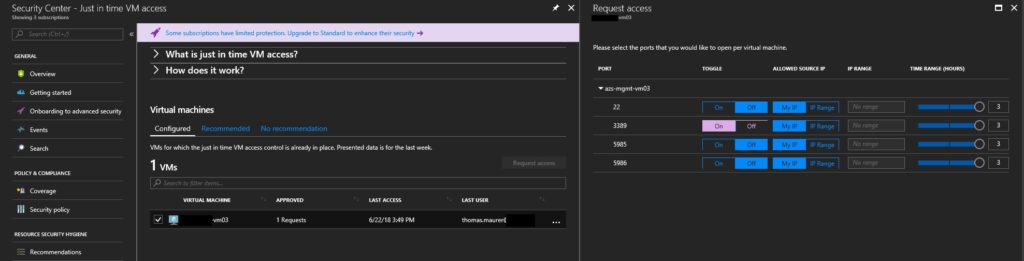
Requesting Just in time VM Access for Azure Virtual Machine
On the Configured section, you can select the VM you want to request access to and click on Request access. You can now choose the ports you want to be open for a specific time and a particular IP address. This will open up the ports, and after 2-3 minutes, you will be able to access the virtual machine.
To send such a request, the user who requests access to the Virtual Machine needs to have write access to the virtual machines in the Azure Role-Based Access Control (RBAC).
Auditing access activity
Of course, all the request get logged and can be reviewed in the Activity Log.
Licensing
Azure just in time VM access is licensed over Azure Security Center and needs the Standard Tier to be enabled for the specific virtual machine.
I hope this gives you an idea of how you can leverage Just in time VM access in Azure for your workloads.
Tags: Access, Azure, Azure JIT, Azure VM, Cloud, JIT, JIT VM access, Just in time VM Access, Microsoft, Microsoft Azure, PowerShell, RDP, SSH, Virtual Machine, VM Last modified: June 10, 2019







thanks for the elaboration, it is really good to understand JIT easily however it would be really good if you could post the vedios as well.
How can I give permission to users who want RDP access without to ask me to enable JIT, and without to give the users to overkill rights?