Create a Windows 10 development virtual machine
If you want to create a Windows 10 development virtual machine (VM) on your Windows 10 device, Microsoft Hyper-V with the quick start...
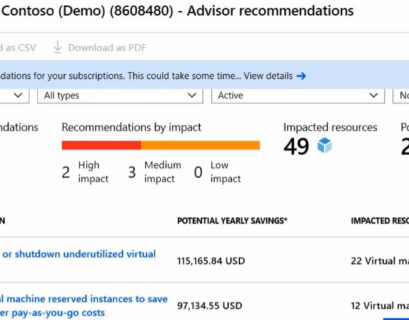
Azure Advisor: How to Improve performance, security, and reliability of your Azure VMs
Running virtual machines in Azure is great. However, there are a lot of things you need to think about to improve performance, security,...
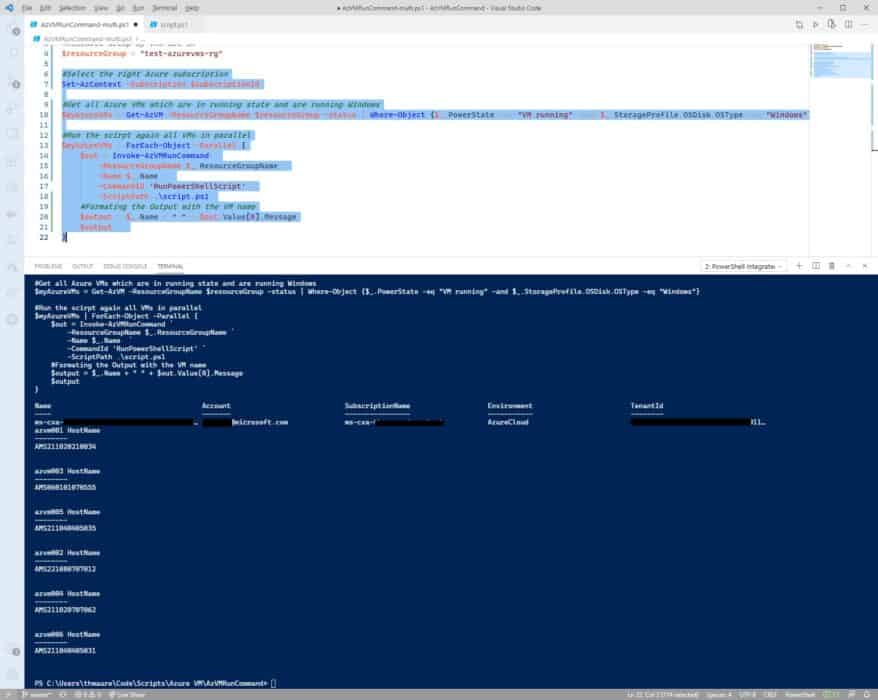
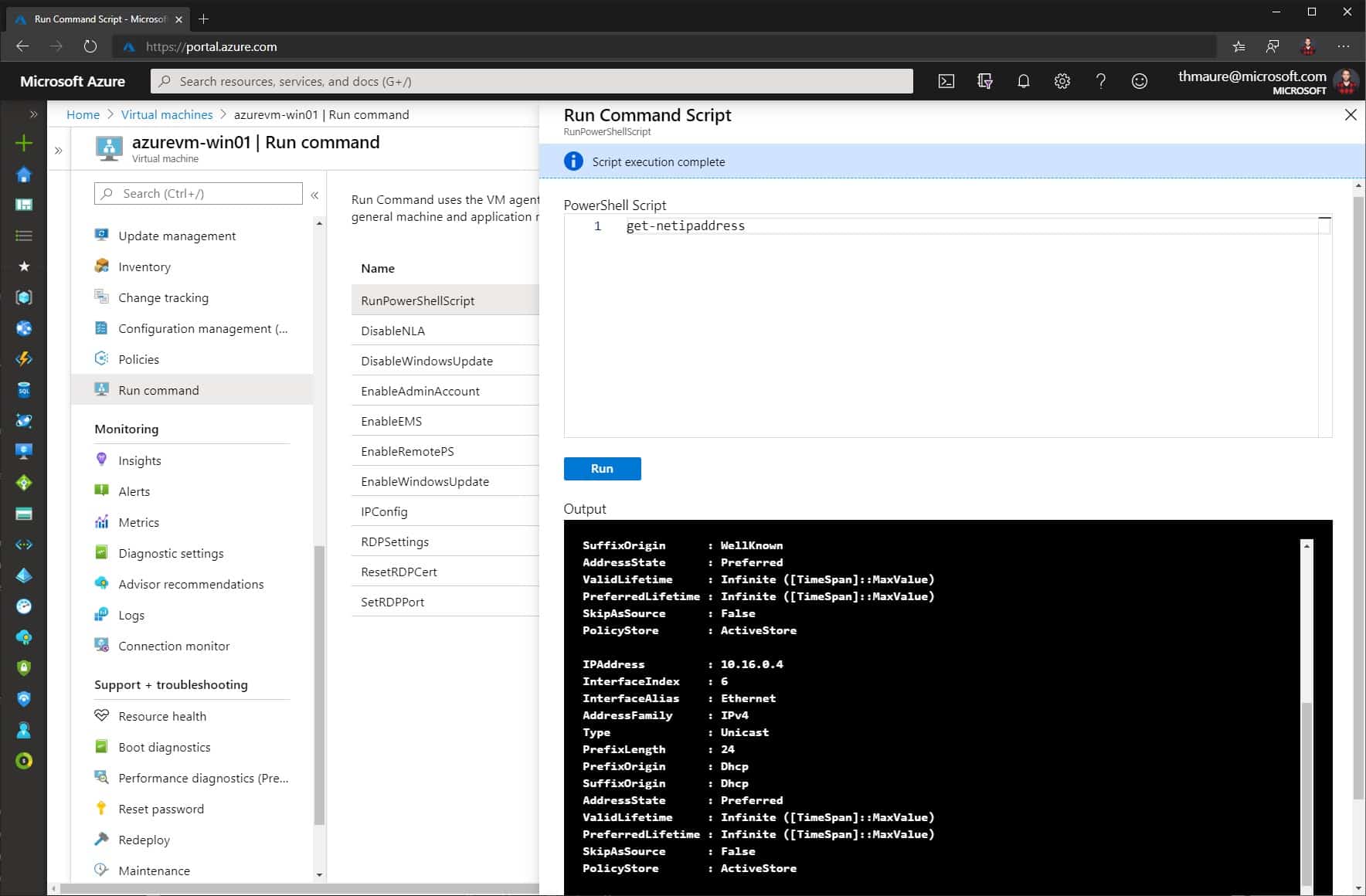
How to run scripts against multiple Azure VMs by using Run Command
I wrote a blog post on how to run scripts in your Azure VM by using Run Command, and explained how...
How to check the available VM Sizes (SKUs) by Azure Region
Do you want to know which Azure VM (virtual machine) sizes are available in an Azure region? Here are some simple ways like the Azure...
Learn about Windows Server Hyper-V and Virtualization
As you know, my background is doing a lot of datacenter and virtualization projects using Hyper-V and System Center. I often get asked, how...
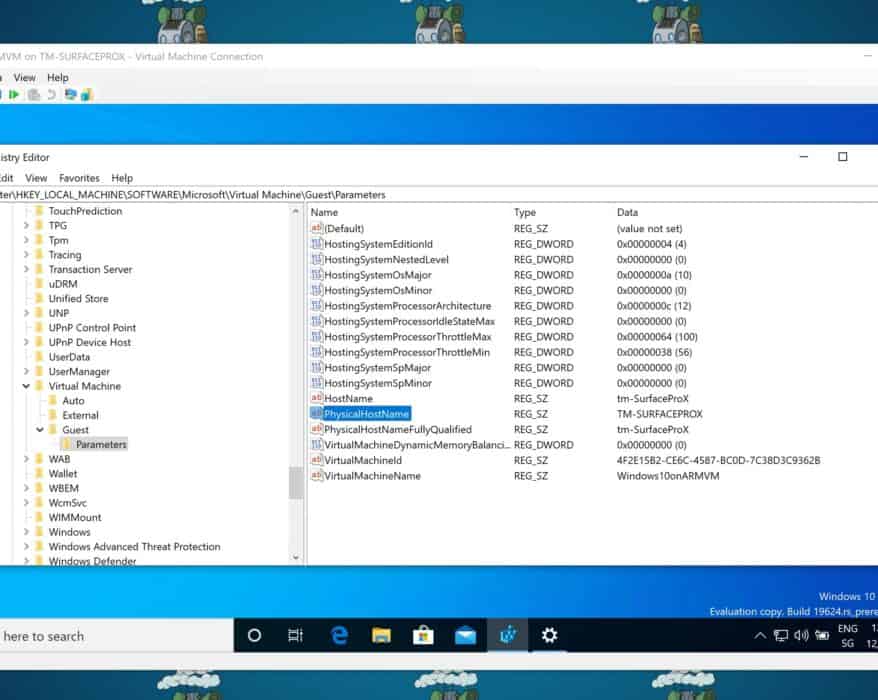
Find the Hostname of a Hyper-V VM
If you are running a virtual machine (VM) on Hyper-V, sometimes you want to know on which Hyper-V...
How to Monitor an Azure virtual machine with Azure Monitor
This week in the Azure tip video, we are going to have a look at how to monitor an Azure virtual machine (VM) with Azure Monitor. You can...
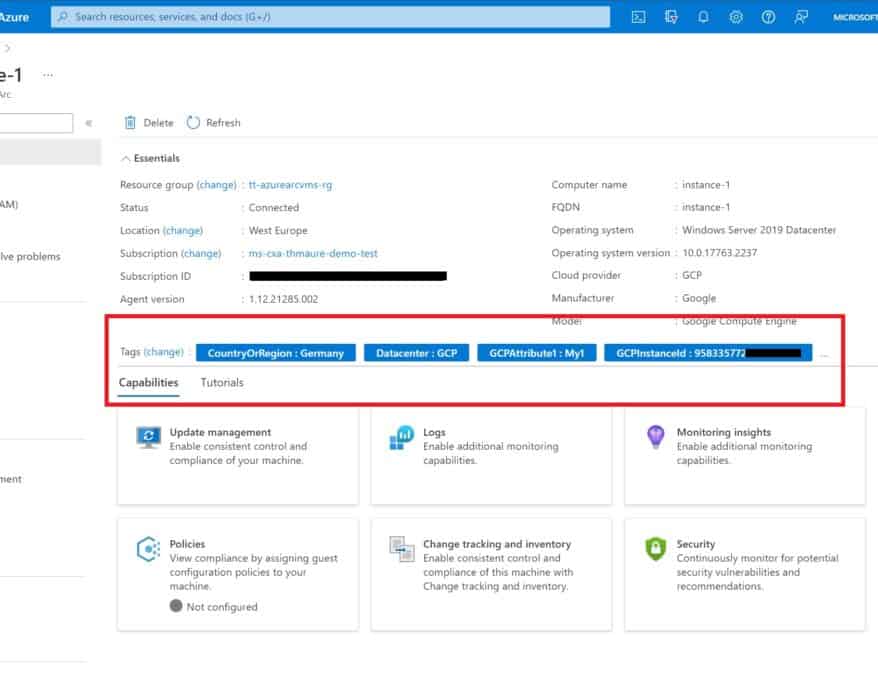
Manage updates and patches for your Azure VMs
In this week’s Azure tip video we are going to have a look at how to manage updates and patches for your Azure virtual machines...
How to Run Scripts in your Azure VM using Run Command
You can access your Azure IaaS virtual machine (VM) in multiple ways like SSH or RDP, depending on...