Speaking at the Windows Server Summit 2024
Today I am proud to share that I will be speaking at the Microsoft Windows Server Summit 2024. The...
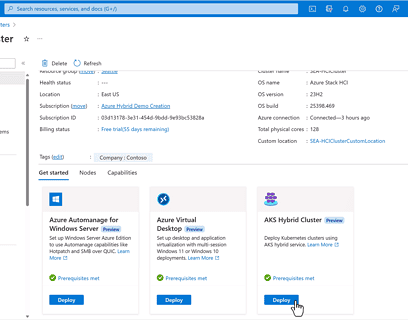
Azure Hybrid, Edge, Adaptive Cloud News from Microsoft Ignite
Today I’m going to share with you some of the exciting Azure hybrid, multicloud, and edge news from Microsoft Ignite 2023, the annual...
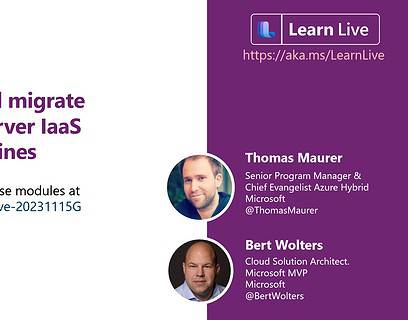
Upgrade and migrate Windows Server IaaS virtual machines at Microsoft Ignite
Today at Microsoft Ignite 2023, I will be presenting Upgrade and migrate Windows Server IaaS virtual machines on an interactive Learn Live...
Microsoft Ignite 2023 – Hybrid, multicloud, and Edge sessions
Microsoft Ignite 2023 will be held from November 15 to November 17 with some great sessions around...
Happy 30th Birthday Windows Server! 🥳🎂🍾🎈
Windows Server just celebrates the 30th birthday! 🥳🎂🍾🎈 Can you believe it? It’s been 30 years since Windows Server...
Hotpatching for Windows Server VMs on Azure with Desktop Experience
This week Microsoft announced the the General Availability of Hotpatching on Windows Server 2022 Datacenter: Azure Edition VMs with Desktop...
Windows Server Summit 2022: Modernize your Apps with Windows Containers and AKS
Rick Claus created a director’s cut of the 2022 Windows Server Summit. One of the sessions...
How to Move Files with PowerShell
PowerShell is a powerful scripting language that can help you automate various tasks on your Windows and Linux system. One of the common...
Connect your AKS Edge Essentials cluster to Azure Arc
In a blog post I was describing how you can install Kubernetes on Windows 10 and Windows 11 using Azure Kubernetes Service (AKS) Edge...
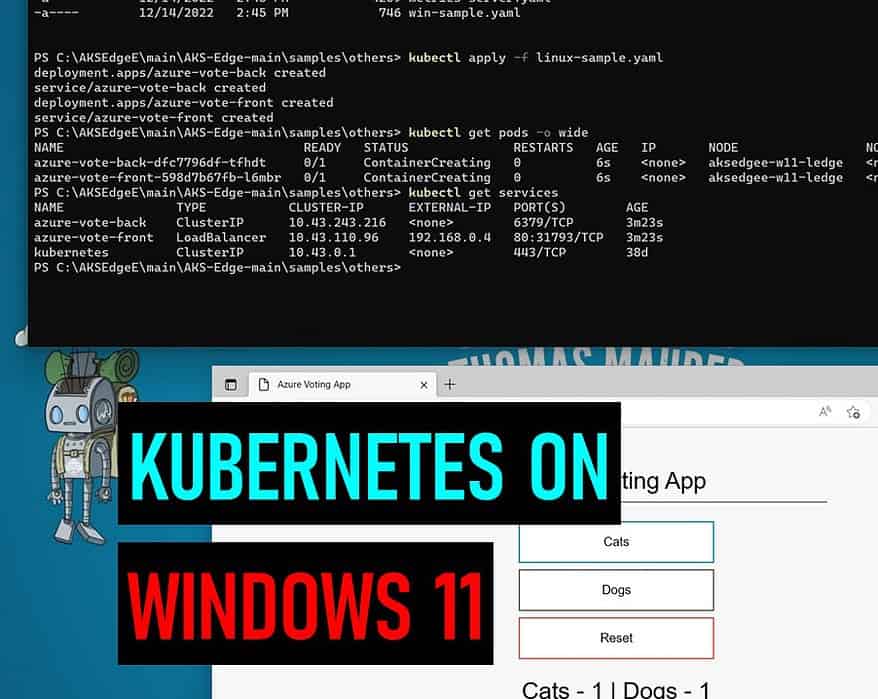
Install Kubernetes on Windows 10 and Windows 11 with AKS Edge Essentials
Awhile back I created a blog post on how you can install Kubernetes on Windows Server, and since...