In this blog post we are going to have a look at how you can use the Azure Arc provided Azure Active Directory (Azure AD) managed identity (MSI) to authenticate in Azure PowerShell on your on-premises Linux and Windows Server machines.
The moment you want to run some automation directly on your servers, you often end up in a scenario where you need some credentials to run your PowerShell script. Now the issue with that is that you need to store or get your credentials from somewhere and that can be an issue. Luckly, Azure Arc provides you with an Azure Active Directory Managed Identity which can be used for that.
Azure PowerShell allows you an uncomplicated way to login using that managed identity.
Prerequisites
- On Windows, you must be a member of the local Administrators group or the Hybrid Agent Extension Applications group.
- On Linux, you must be a member of the himds group.
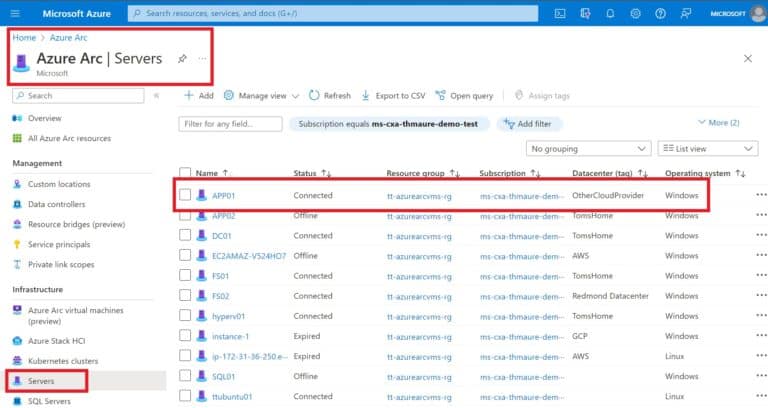
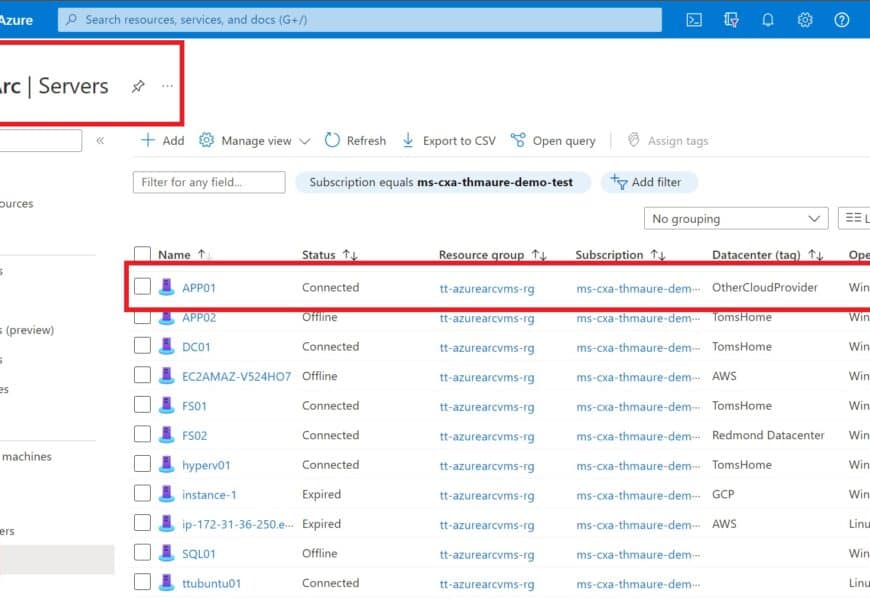
- I connected my servers to Azure using Azure Arc enabled servers and installed the Azure connected machine agent.
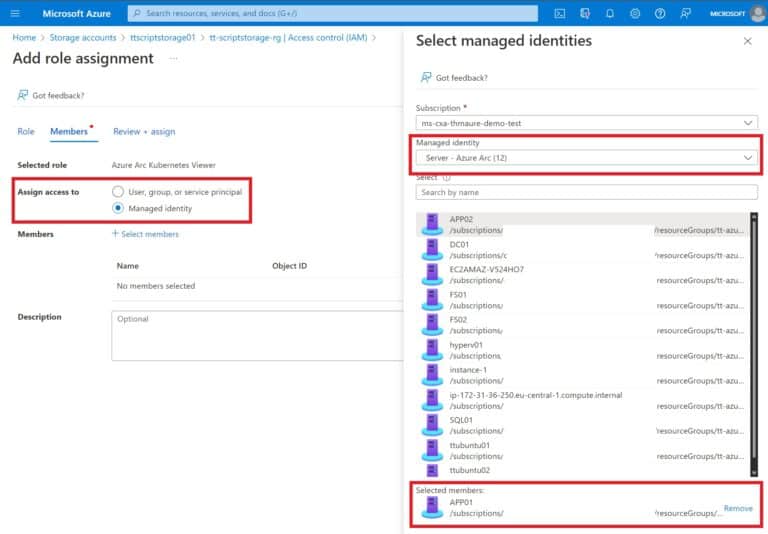
- You are a member of the Owner group in the subscription or resource group, in order to perform required resource creation and role management steps.
- Have Azure PowerShell installed, depending on what you are planning to use.
Get an access token using REST API
For an Azure Arc-enabled Windows server, using PowerShell, you invoke the web request to get the token from the local host in the specific port. Specify the request using the IP address or the environmental variable IDENTITY_ENDPOINT.
$apiVersion = "2020-06-01"
$resource = "https://management.azure.com/"
$endpoint = "{0}?resource={1}&api-version={2}" -f $env:IDENTITY_ENDPOINT,$resource,$apiVersion
$secretFile = ""
try
{
Invoke-WebRequest -Method GET -Uri $endpoint -Headers @{Metadata='True'} -UseBasicParsing
}
catch
{
$wwwAuthHeader = $_.Exception.Response.Headers["WWW-Authenticate"]
if ($wwwAuthHeader -match "Basic realm=.+")
{
$secretFile = ($wwwAuthHeader -split "Basic realm=")[1]
}
}
Write-Host "Secret file path: " $secretFile`n
$secret = cat -Raw $secretFile
$response = Invoke-WebRequest -Method GET -Uri $endpoint -Headers @{Metadata='True'; Authorization="Basic $secret"} -UseBasicParsing
if ($response)
{
$token = (ConvertFrom-Json -InputObject $response.Content).access_token
Write-Host "Access token: " $token
}For an Azure Arc-enabled Linux server, using Bash, you invoke the web request to get the token from the local host in the specific port. Specify the following request using the IP address or the environmental variable IDENTITY_ENDPOINT. To complete this step, you need an SSH client.
ChallengeTokenPath=$(curl -s -D - -H Metadata:true "http://127.0.0.1:40342/metadata/identity/oauth2/token?api-version=2019-11-01&resource=https%3A%2F%2Fmanagement.azure.com" | grep Www-Authenticate | cut -d "=" -f 2 | tr -d "[:cntrl:]")
ChallengeToken=$(cat $ChallengeTokenPath)
if [ $? -ne 0 ]; then
echo "Could not retrieve challenge token, double check that this command is run with root privileges."
else
curl -s -H Metadata:true -H "Authorization: Basic $ChallengeToken" "http://127.0.0.1:40342/metadata/identity/oauth2/token?api-version=2019-11-01&resource=https%3A%2F%2Fmanagement.azure.com"
fiYou can learn more about this on Microsoft Learn.
Login with Azure PowerShell on Azure Arc enabled server using Managed Identity
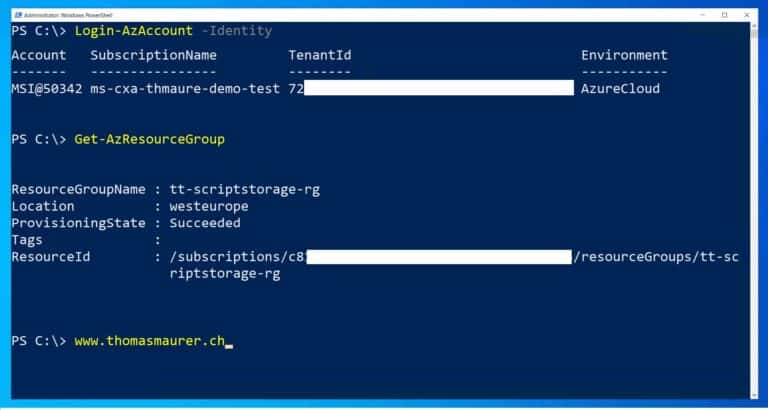
To login with your managed identity using Azure PowerShell, run the following command:
Connect-AzAccount -IdentityNow you have access to the resources your Azure AD managed identity (MSI) on your Azure Arc-enabled server has permissions to.
Conclusion
I hope this post is helpful to build some automation with Azure PowerShell on your on-premises or multi-cloud servers with Azure Arc. Let me know if you have any questions in the comments below.
Tags: Azure, Azure AD, Cloud, Hybrid, Hybrid Cloud, Linux, Managed Identity, Microsoft, Microsoft Azure, PowerShell, Virtualization, Windows, Windows Server Last modified: October 6, 2022






Hi,
Great posts about Azure Arc and other stuff.
I wonder if there is some kind of “Arc Agent Gateway” to enable onboarding of servers that don’t have an internet connection? To my understanding only Direct Connection or Private Link setups are only supported.
– Direct Connection encrypted on outgoing port 443 to some selected Azure APIs
– Proxy Support
– And Private Link
Where you need a central place to connect, customers usually use Private Link.
Announcing the Public Preview of the Azure Arc gateway! | Microsoft Community Hub
https://techcommunity.microsoft.com/blog/azurearcblog/announcing-the-public-preview-of-the-azure-arc-gateway/4292278
Nov 15, 2024
Great Article! This method allows us to connect an Azure Arc enabled Server to Storage Account, Key Vault and all the other Azure Services.
Thanks, yes this is great for this! Thanks for the comment :)