A year ago Microsoft announced that they were working on a new technology in Azure to protect and encrypt data in use, called Azure Confidential Computing. If you are moving sensitive data to the cloud, you also want to encrypt it. Today, you can do this for data in transit and data at rest. However, data in use is a challenge. Azure Confidential Computing addresses precisely that scenario and helps you to encrypt data in use. Microsoft was running a private preview program in the last year, and at Microsoft Ignite this year, Microsoft opened up a public preview.
What is Azure Confidential Computing
Azure Confidential Computing together with Intel SGX technology, addresses the following threads:
- Malicious insiders with administrative privilege or direct access to hardware on which it is being processed
- Hackers and malware that exploit bugs in the operating system, application, or hypervisor
- Third parties accessing it without their consent
There are ways to secure data at rest and in transit, but you need to protect your data from threats as it’s being processed. Now you can. Confidential computing adds new data security capabilities using trusted execution environments (TEEs) or encryption mechanisms to protect your data while in use. TEEs are hardware or software implementations that safeguard data being processed from access outside the TEE. The hardware provides a protected container by securing a portion of the processor and memory. Only authorized code is permitted to run and to access data, so code and data are protected against viewing and modification from outside of TEE.
With Azure Confidential Computing, you can now fully protect your data in transit, at rest, and in use. To get some more information about Azure Confidential Computing, you can watch this video from Mark Russinovich:
Supported Azure VM Sizes
For Azure Confidential Computing, Microsoft introduced a new VM type called DC-series. While these virtual machines may ‘look and feel’ like standard VM sizes from the control plane, they are backed by hardware-based Trusted Execution Environments (TEEs), specifically the latest generation of Intel Xeon Processors with Intel SGX technology. Azure Confidential Computing is not only available for virtual machines; it is and will also be available for other Azure services like SQL or Blockchain.
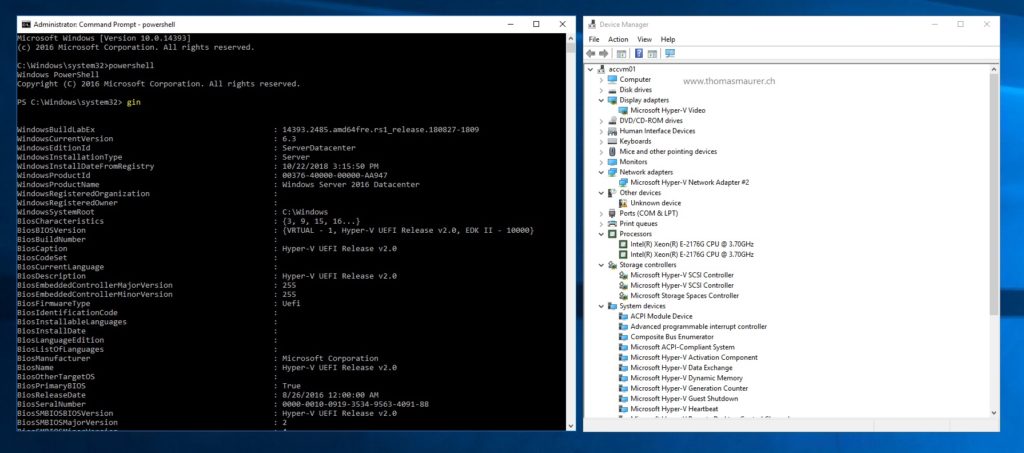
As Aidan Finn mentions in his blog post, the DC-series are the first Hyper-V Generation 2 Virtual Machines running in Azure.
Getting Started with Confidential Computing
To get started with Azure Confidential Computing, I recommend that you read the blog post from Christine Avanessians (Principal PM Manager, Microsoft Azure).
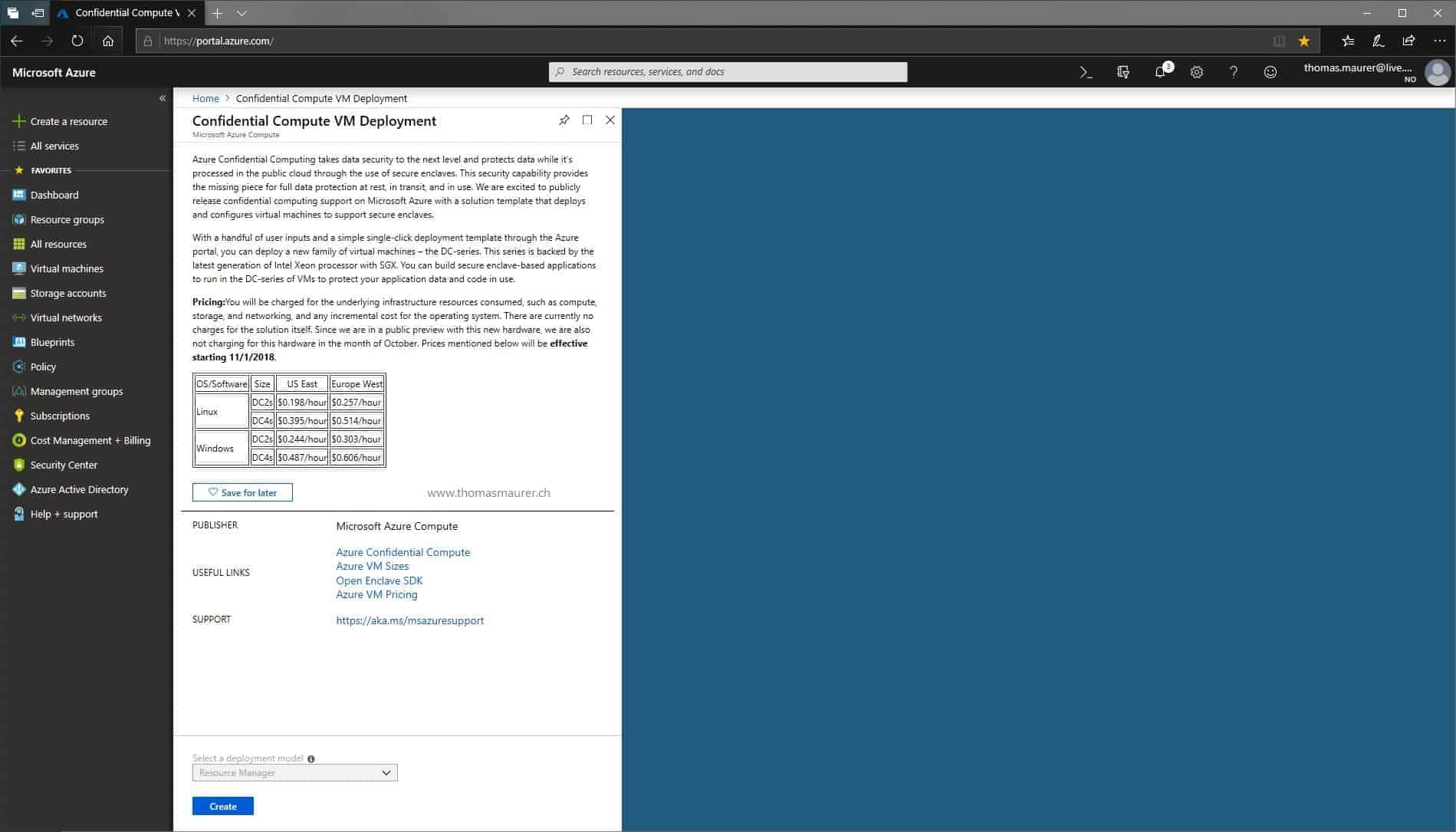
- The easiest way is to deploy the VM from the Azure Marketplace.
- Today East US and West Europe are supported Azure Regions during the preview.
- Since these are Generation 2 VMs, they need a custom OS Image, today you can use Windows Server 2016 Datacenter and Ubuntu Server 16.04
Let me know if you have any questions and leave a comment.
Tags: Azure, Azure Confidential Computing, Azure Generation 2 VMs, Azure Marketplace, Confidential Computing, encryption in use, Generation 2 VMs, Intel SGX, Microsoft, TEE, Ubuntu, Ubuntu Server, VM Encryption, Windows Server 2016 Last modified: May 28, 2019