Microsoft very quickly responded to the speculative execution side-channel vulnerabilities also called Meltdown and Spectre which affect many modern processors and operating systems, including chipsets from Intel, AMD, and ARM. Microsoft released some guidance how you should protect your devices against these vulnerabilities. The Microsoft Security Defense Team also published an article with guidance and more details on this: ADV180002 | Guidance to mitigate speculative execution side-channel vulnerabilities
In this blog post I tried to quickly summarize the information and link it to the right websites.
Summary
Microsoft is aware of detailed information that has been published about a new class of vulnerabilities referred to as speculative execution side-channel attacks. This industry-wide attack method takes advantage of out-of-order execution on many modern microprocessors and is not restricted to a single chip, hardware manufacturer, or software vendor. To be fully protected, updates are required at many layers of the computing stack and include software and hardware/firmware updates. Microsoft has collaborated closely with industry partners to develop and test mitigations to help provide protections for our customers. At the time of publication, Microsoft had not received any information to indicate that these vulnerabilities have been used to attack our customers.
Note This issue also affects other operating systems, such as Android, Chrome, iOS, and MacOS.
Warning
Microsoft addressed protect against speculative execution side-channel vulnerabilities in the latest Windows Updates. However, customers who only install the Windows January 2018 security updates will not receive the benefit of all known protections against the vulnerabilities. In addition to installing the January security updates, a processor microcode, or firmware, update is required. This should be available through your device manufacturer. Surface customers will receive a microcode update via Windows update.
Guidance for Windows Client
Customers should take the following actions to help protect against the vulnerabilities:
- Verify that you are running a supported antivirus application before you install OS or firmware updates. Contact the antivirus software vendor for compatibility information.
- Apply all available Windows operating system updates, including the January 2018 Windows security updates.
- Apply the applicable firmware update that is provided by the device manufacturer
Windows-based machines (physical or virtual) should install the Microsoft security updates that were released on January 3, 2018. See Microsoft Security Advisory ADV180002 for updates for the following versions of Windows.
Read full guidance for Windows Client here: Windows Client Guidance for IT Pros to protect against speculative execution side-channel vulnerabilities
Guidance for Windows Server
Customers should take the following actions to help protect against the vulnerabilities:
- Apply the Windows operating system update. For details on how to enable this update, see Microsoft Knowledge Base Article 4072699.
- Make necessary configuration changes to enable protection.
- Apply an applicable firmware update from the OEM device manufacturer.
Windows Servers-based machines (physical or virtual) should get the Windows security updates that were released on January 3, 2018, and are available from Windows Update.
- Windows Server, version 1709 (Server Core Installation) KB4056892
- Windows Server 2016 KB4056890
- Windows Server 2012 R2 KB4056898
- Windows Server 2012 Not available yet
- Windows Server 2008 R2 KB4056897
Your server is at increased risk if it is in one of the following categories:
- Hyper-V hosts
- Remote Desktop Services Hosts (RDSH)
- For physical hosts or virtual machines that are running untrusted code such as containers or untrusted extensions for database, untrusted web content or workloads that run code that is provided from external sources.
There for Microsoft posted some additional registry keys to mitigations on servers. Microsoft also added some extra registry keys if you are running older versions of Hyper-V.
Read the full guidance for Windows Server and the registry keys here: Windows Server guidance to protect against speculative execution side-channel vulnerabilities
Guidance for Virtual Machines running on Hyper-V
In addition to this guidance, the following steps are required to ensure that your virtual machines are protected from CVE-2017-5715 (branch target injection):
- Ensure guest virtual machines have access to the updated firmware. By default, virtual machines with a VM version below 8.0 will not have access to updated firmware capabilities required to mitigate CVE-2017-5715. Because VM version 8.0 is only available starting with Windows Server 2016, users of Windows Server 2012 R2 or earlier must modify a specific registry value on all machines in their cluster.
- Perform a cold boot of guest virtual machines.Virtual machines will not see the updated firmware capabilities until they go through a cold boot. This means the running VMs must completely power off before starting again. Rebooting from inside the guest operating system is not sufficient.
- Update the guest operating system as required. See guidance for Windows Server.
Read the full guidance for Guest Virtual Machines here: Protecting guest virtual machines from CVE-2017-5715 (branch target injection)
Guidance for Surface Devices
Microsoft will provide UEFI updates for the following devices:
- Surface Pro 3
- Surface Pro 4
- Surface Book
- Surface Studio
- Surface Pro Model 1796
- Surface Laptop
- Surface Pro with LTE Advanced
- Surface Book 2
The updates will be available for the above devices running Windows 10 Creators Update (OS version 15063) and Windows 10 Fall Creators Update (OS version 16299). You will be able to receive these updates through Windows Update or by visiting the Microsoft Download Center.
Read full guidance for Surface Devices here: Surface Guidance for Customers and Partners: Protect your devices against the recent chip-related security vulnerability
Guidance for Azure
Microsoft has already deployed mitigations across the majority of our cloud services and is accelerating efforts to complete the remainder.
However, I always recommend that you also patch your operating systems and applications to be protected against other vulnerabilities.
Impact to Enterprise Cloud Services
Microsoft is not aware of any attacks on the Microsoft Cloud customers which leverage these types of vulnerabilities. Microsoft employs a variety of detection capabilities to quickly respond to any malicious activity in our enterprise cloud services.
Most of the Azure infrastructure has already received mitigations against this class of vulnerability. An accelerated reboot is occurring for any remaining hosts. Customers can check the Azure Portal for additional details.
All other enterprise cloud services such as Office 365, Dynamics 365, and Enterprise Mobility + Security have mitigations against these types of vulnerabilities. Microsoft engineering is continuing to perform analysis across the environments to confirm further protection.
Read full guidance for Microsoft Azure here: Microsoft Cloud Protections Against Speculative Execution Side-Channel Vulnerabilities
Guidance for Azure Stack
Azure Stack customers should take the following actions to help protect the Azure Stack infrastructure against the vulnerabilities:
- Apply Azure Stack 1712 update. See the Azure Stack 1712 update release notes for instructions about how to apply this update to your Azure Stack integrated system.
- Install firmware updates from your Azure Stack OEM vendor after the Azure Stack 1712 update installation is completed. Refer to your OEM vendor website to download and apply the updates.
- Some variations of these vulnerabilities apply also to the virtual machines (VMs) that are running in the tenant space. Customers should continue to apply security best practices for their VM images, and apply all available operating system updates to the VM images that are running on Azure Stack. Contact the vendor of your operating systems for updates and instructions, as necessary. For Windows VM customers, guidance has now been published and is available in this Security Update Guide.
Read full guidance for Microsoft Azure Stack here: Azure Stack guidance to protect against the speculative execution side-channel vulnerabilities
Guidance for SQL Server
The following versions of Microsoft SQL Server are impacted by this issue when running on x86 and x64 processor systems:
- SQL Server 2008
- SQL Server 2008 R2
- SQL Server 2012
- SQL Server 2014
- SQL Server 2016
- SQL Server 2017
IA64-based versions of SQL Server 2008 are not believed to be affected.
Microsoft made a list of different SQL Server scenarios depending on the environment that SQL Server is running in and what functionality is being used. Microsoft recommends that you deploy fixes by using normal procedures to validate new binaries before deploying them to production environments.
You can finde the list for scenarios and recommendations here: SQL Server guidance to protect against speculative execution side-channel vulnerabilities
There is also a list of updates for SQL Server available:
- 4057122 Description of the security update for SQL Server 2017 GDR: January 3, 2018
- 4058562 Description of the security update for SQL Server 2017 CU3 RTM: January 3, 2018
- 4058561 Description of the security update for SQL Server 2016 CU7 SP1: January 3, 2018
- 4057118 Description of the security update for SQL Server 2016 GDR SP1: January 3, 2018
- 4058559 Description of the security update for SQL Server 2016 CU: January 6, 2018
- 4058560 Description of the security update for SQL Server 2016 GDR: January 6, 2018
- 4057114 Description of the security update for SQL Server 2008 SP4 GDR: January 6, 2018
- 4057113 Description of the security update for SQL Server 2008 SP3 R2 GDR: January 6, 2018
Read the full guidance for SQL Server here: SQL Server guidance to protect against speculative execution side-channel vulnerabilities
Verifying protections again speculative execution side-channel vulnerabilities
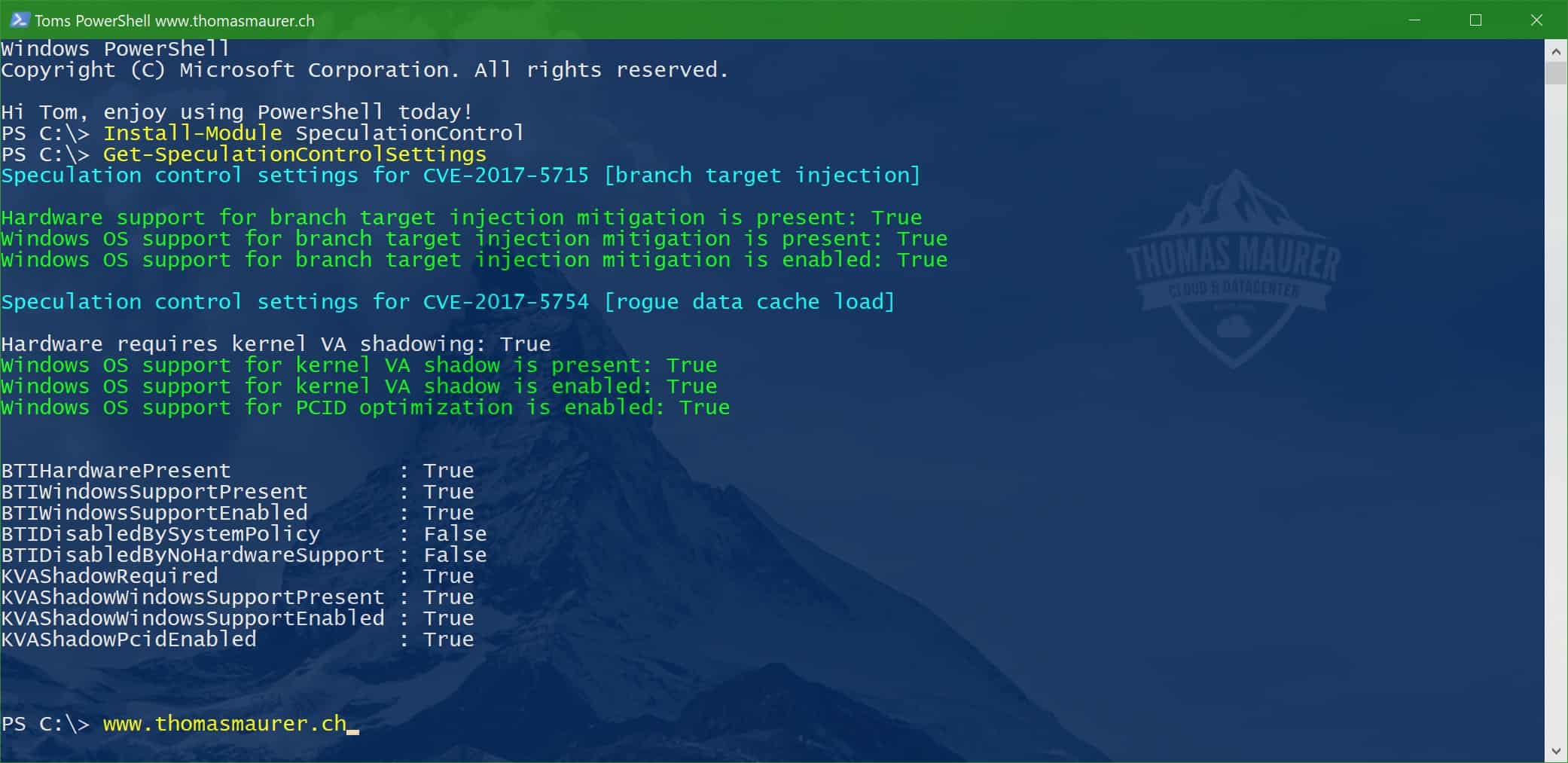
The Microsoft Security Response Center released a PowerShell Module on the PowerShell Gallery called SpeculationControl, which verifies if your system is protected or not.
You can find more here: Use PowerShell to verifying protections again peculative execution side-channel vulnerabilities CVE-2017-5754 (Meltdown) and CVE-2017-5715 (Spectre)
More information on how to mitigate speculative execution side-channel vulnerabilities can be found here: ADV180002 | Guidance to mitigate speculative execution side-channel vulnerabilities
Tags: AMD, ARM, Azure, Azure Stack, Chipset, Hyper-V, Intel, Meltdown, Microsoft, PowerShell, Spectre, speculative execution side-channel, vulnerabilities, Windows, Windows 10, Windows Server Last modified: February 24, 2018







If my servers run Windows server 2016 with GUI, then should I install KB4056890 or KB4056892?
If it is Windows Sevrer 2016 it is https://support.microsoft.com/en-gb/help/4056890
Thanks Thomas for this article.
On a Win2016 Server in Azure patched with 4056890, the powershell result shows only one line green:
Hardware support for branch target injection mitigation is present: False (red)
Windows OS support for branch target injection mitigation is present: True (green)
Windows OS support for branch target injection mitigation is enabled: False (red)
Windows OS support for branch target injection mitigation is disabled by system policy: True (red)
Windows OS support for branch target injection mitigation is disabled by absence of hardware support: True (red)
Do i have to add the Reg-Key mentioned in the KB-article ? (i know, some of them are bios-related until they will be green).
Thx
Bruno
Looks like this is the normal behavior inside a VM
Hi Thomas, thanks for this article. Which version do I have to install if it’s a Hyper-V Server 2012 R2?
Thanks, Simon
Windows Server 2012 R2 KB4056898 should address the issue for Hyper-V Server 2012 R2. Make sure you also update the BIOS/Firmware
Thomas
Thanks, I was able to patch the Hyper-V Servers, apply the BIOS Update for DL380 G9 and apply the registry fix.
I still have the following output: https://www.bleepstatic.com/images/news/u/986406/Microsoft/Windows10/Meltdown+Spectre-Powershell-post-update.png
What is missing?
On the host or on the VM? Where did you run the script?
The output on the hosts are all green, but not on the VM. I did run the registry script on the VM too.
Seems to be the correct output. The host needs to be all green.