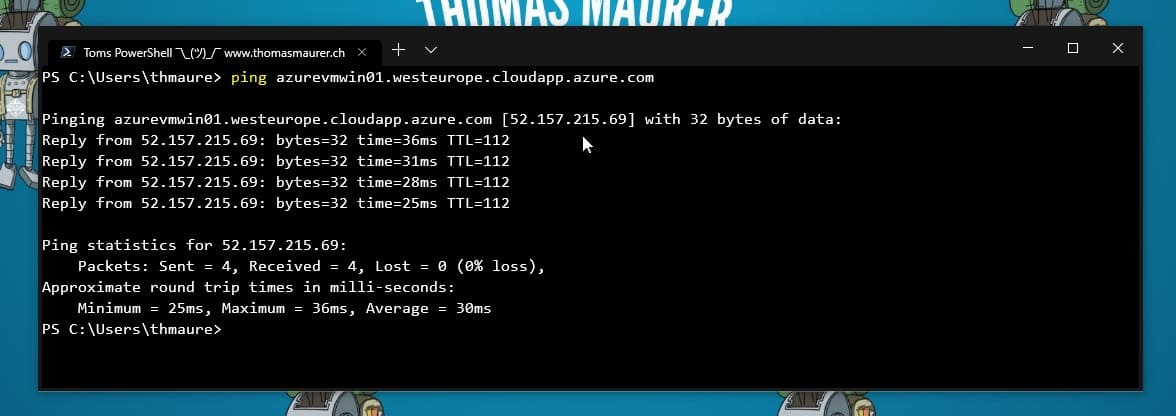
How to enable Ping (ICMP echo) on an Azure VM
This is just a very quick blog post because I got the question from a couple of people. In this...
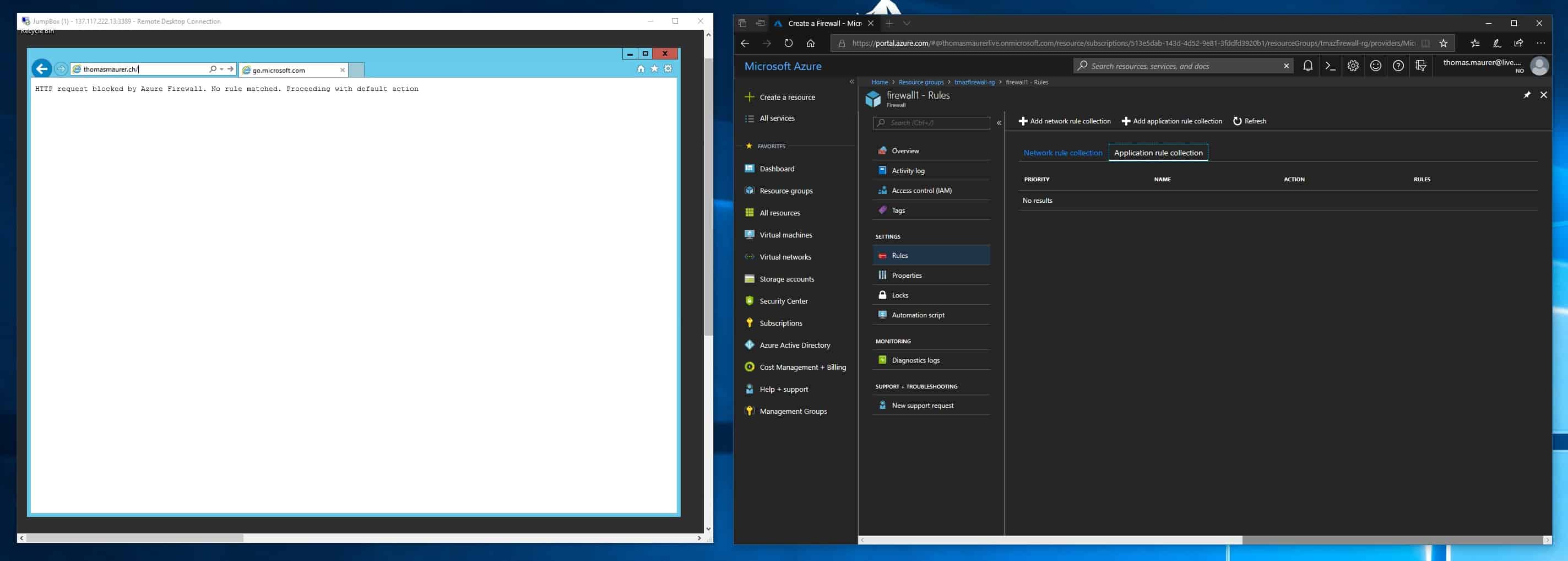
This is the Microsoft Azure Firewall
Last week Microsoft announced some cool new and long awaited Azure Network functionalities, which are now in public preview. One of them is...