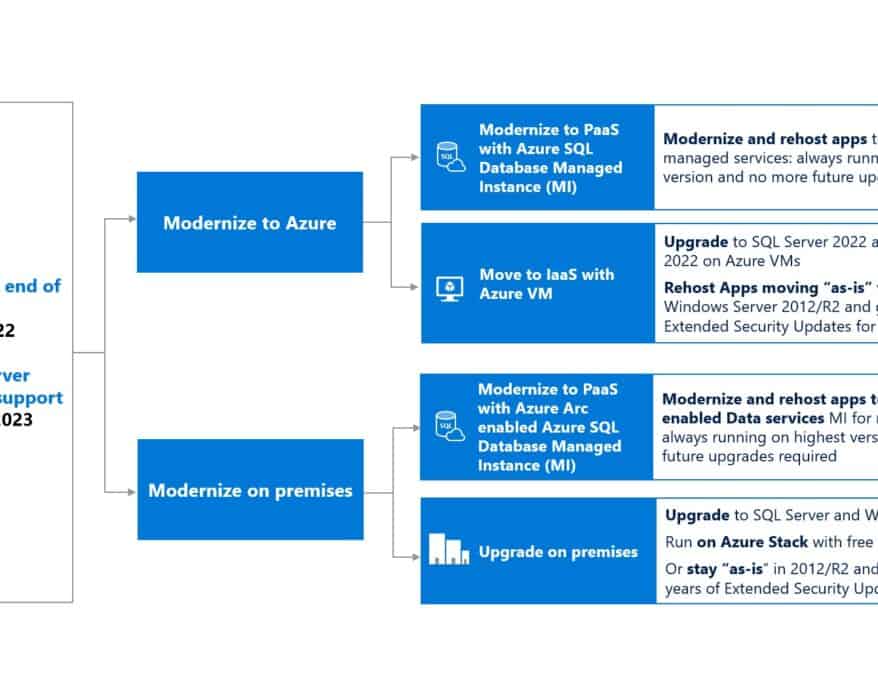
Extended Security Updates for Windows Server and SQL Server in Azure and Azure Stack
Windows Server is an essential workload platform for almost every organization, and is one of the...
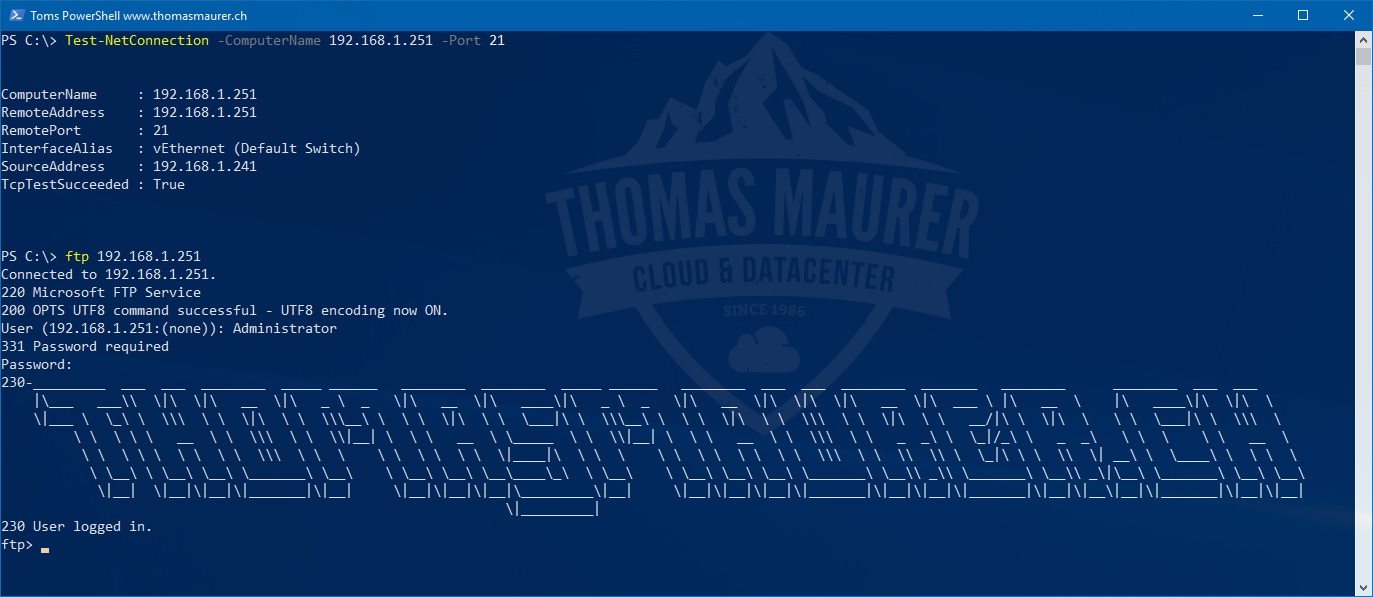
Install FTP Server on Windows Server
Windows Server has IIS build in, which also offers an FTP server option. The File Transfer Protocol (FTP) is still a very popular protocol...
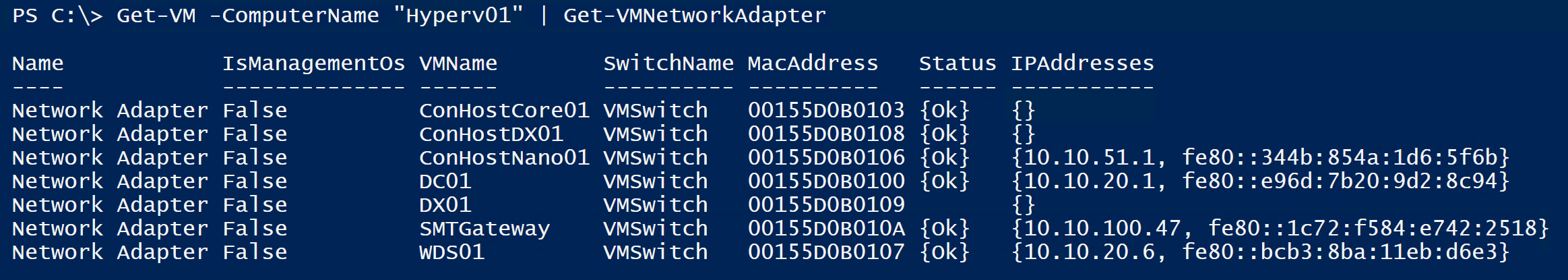
PowerShell One-liner to list IP Addresses of Hyper-V Virtual Machines
Here a very quick PowerShell command to list all the Virtual Network Adapters, including IP Addresses of Virtual Machines running on a...
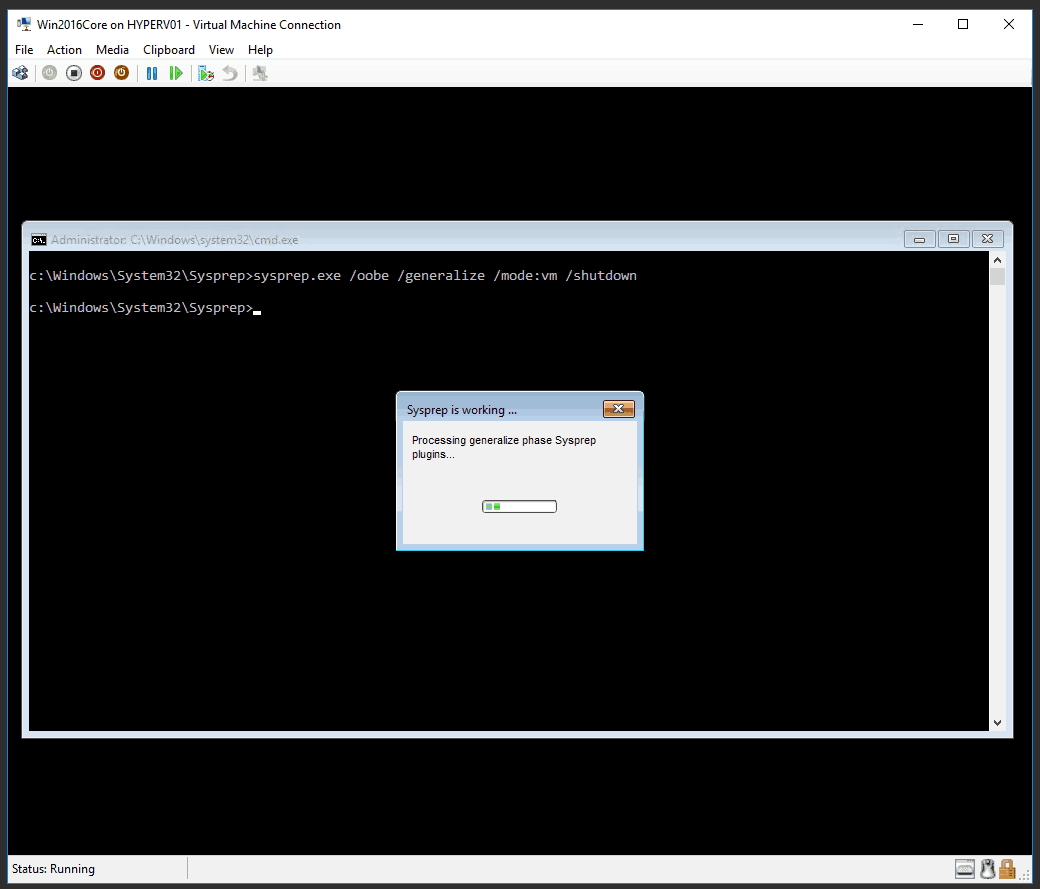
Windows Sysprep for Virtual Machines
For using the same system image for different virtual machines or physical computer, Microsoft...
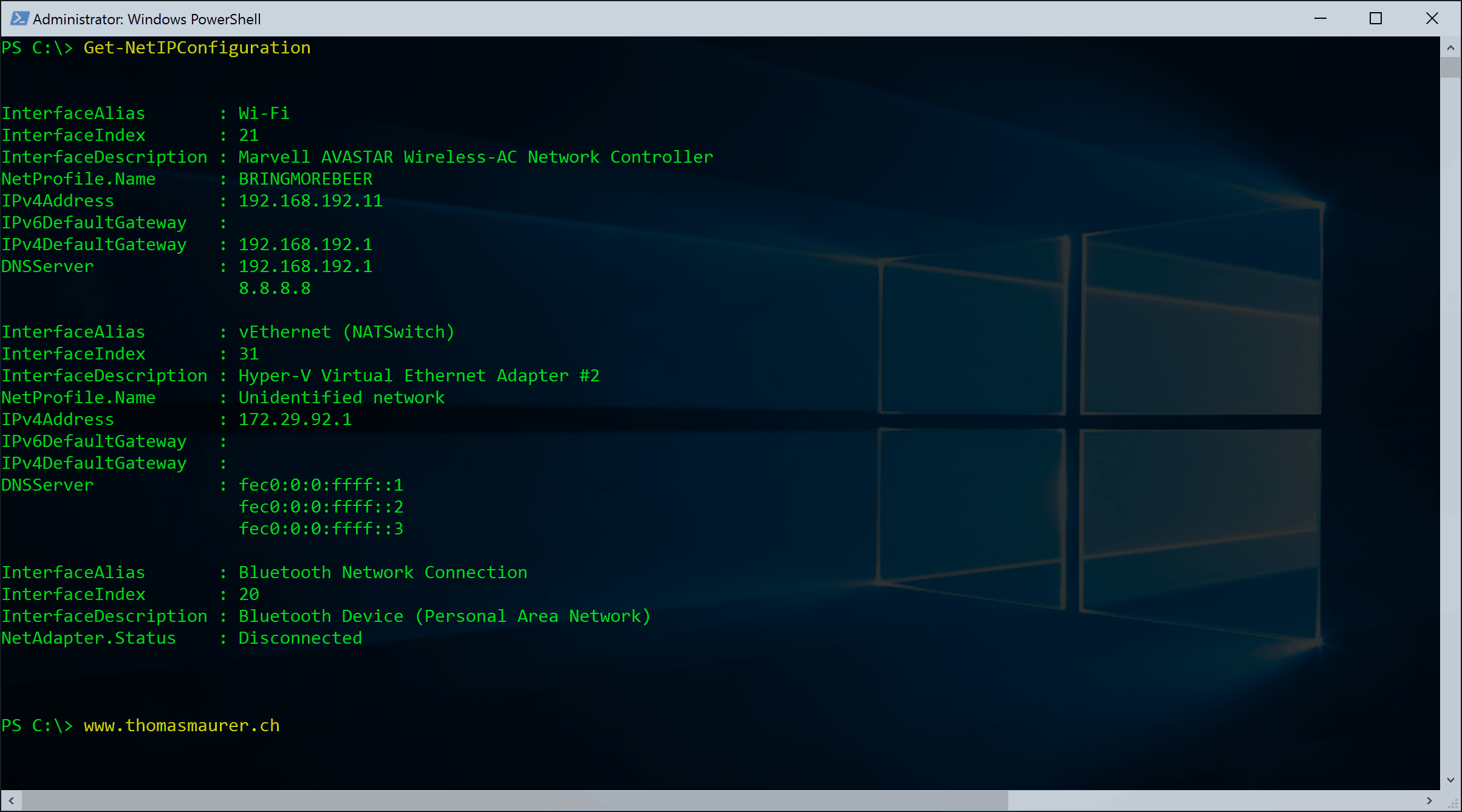
Basic Networking PowerShell cmdlets cheatsheet to replace netsh, ipconfig, nslookup and more
Around 4 years ago I wrote a blog post about how to Replace netsh with Windows PowerShell which includes basic powershell networking...
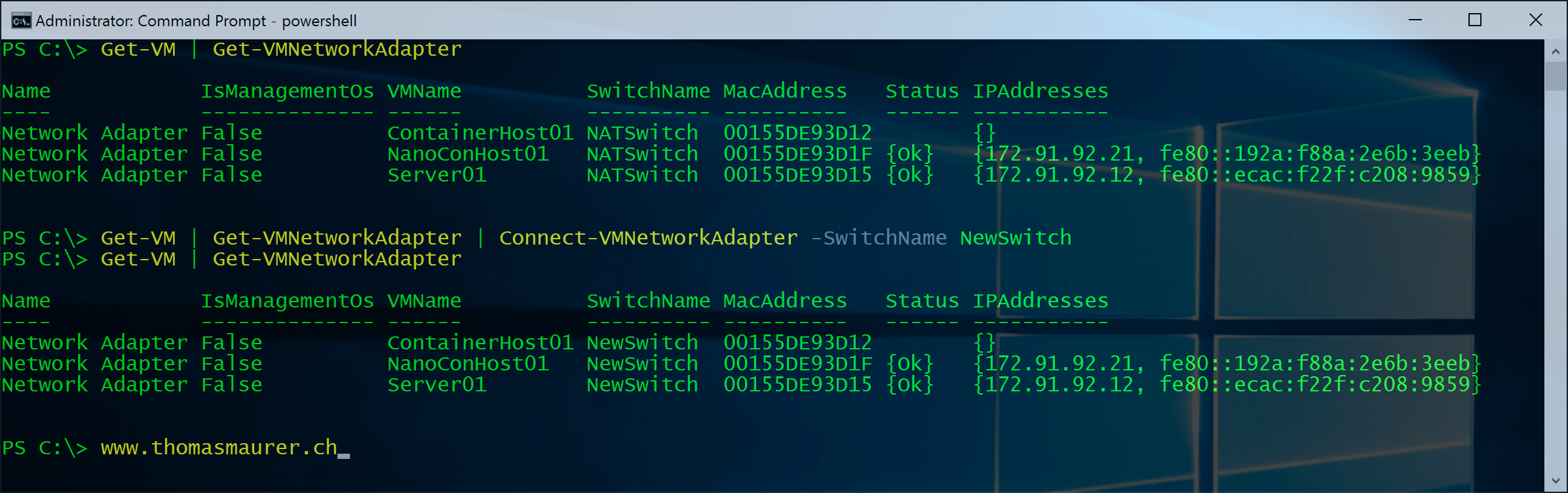
Change Hyper-V VM Switch of Virtual Machines using PowerShell
This is one of the first post of a short blog series with some simple PowerShell scripts and oneliners for Hyper-V. One this is how you...
Move multipe Hyper-V Virtual Machines with Live Storage Migration via Windows PowerShell
Well I was working in on a Private Cloud Deployment where we had some temporary storage for our...
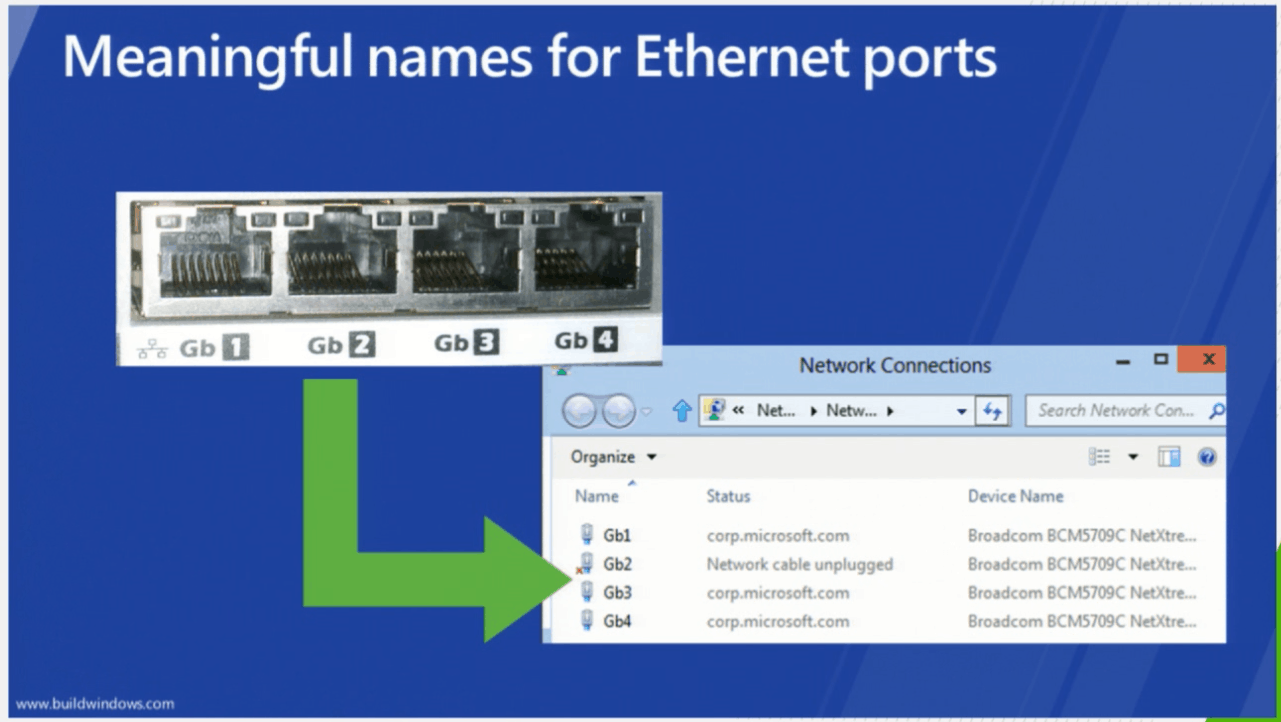
Cisco UCS supports Consistent Device Naming (CDN)
Yesterday I posted about Cisco UCS supporting RDMA (SMB Direct) with firmware version 2.2(4b)B. Walter Dey, former Cisco Distinguished...
Cisco UCS supports RoCE for Microsoft SMB Direct
As you may know we use SMB as the storage protocol for several Hyper-V deployments using Scale-Out File Server and Storage Spaces which...
Overview on Windows Server and Hyper-V 2012 R2 NIC Teaming and SMB Multichannel
I know this is nothing new but since I had to mention the Whitepaper on NIC Teaming and the use of...