Connect Ubiquiti UniFi Dream Machine to Azure VPN
A couple of days ago I got a Ubiquiti UniFi Dream Machine, which is an all-in-one device with an...
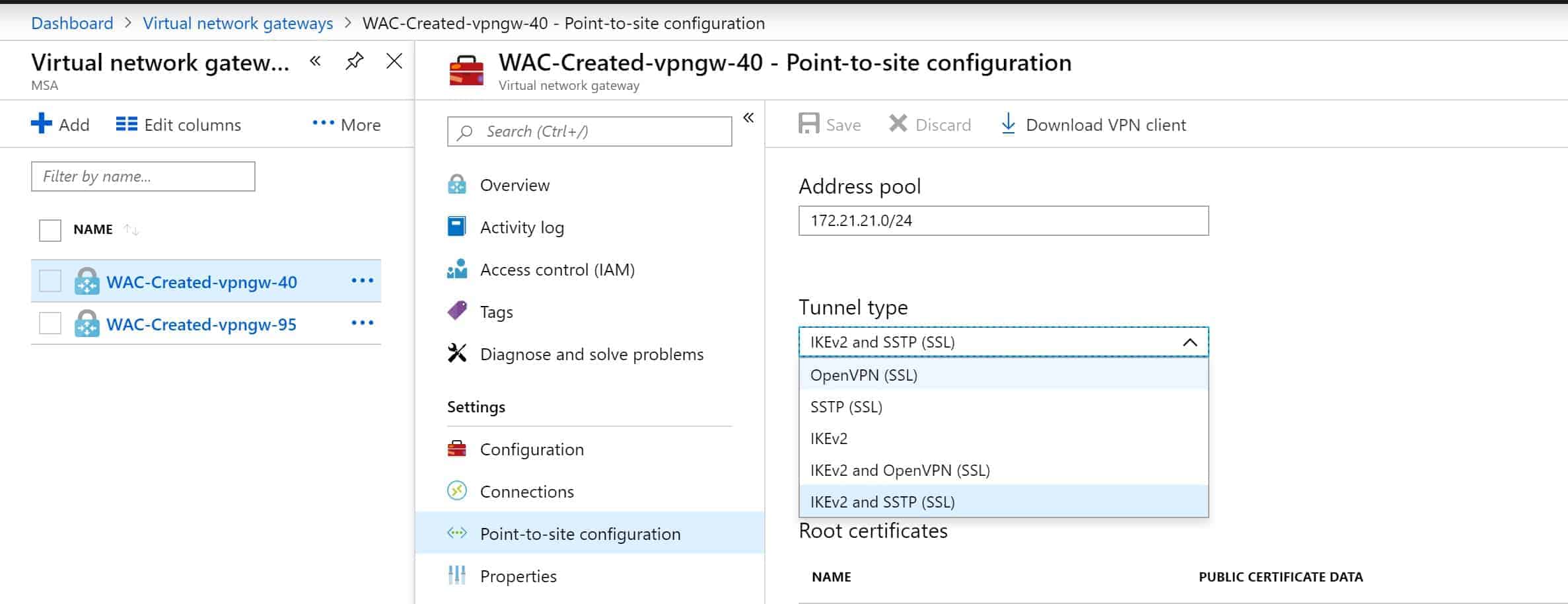
OpenVPN support in Azure VPN gateways
Today, the Azure networking team announced the General Availability (GA) of OpenVPN protocol in Azure VPN gateways for P2S connectivity....
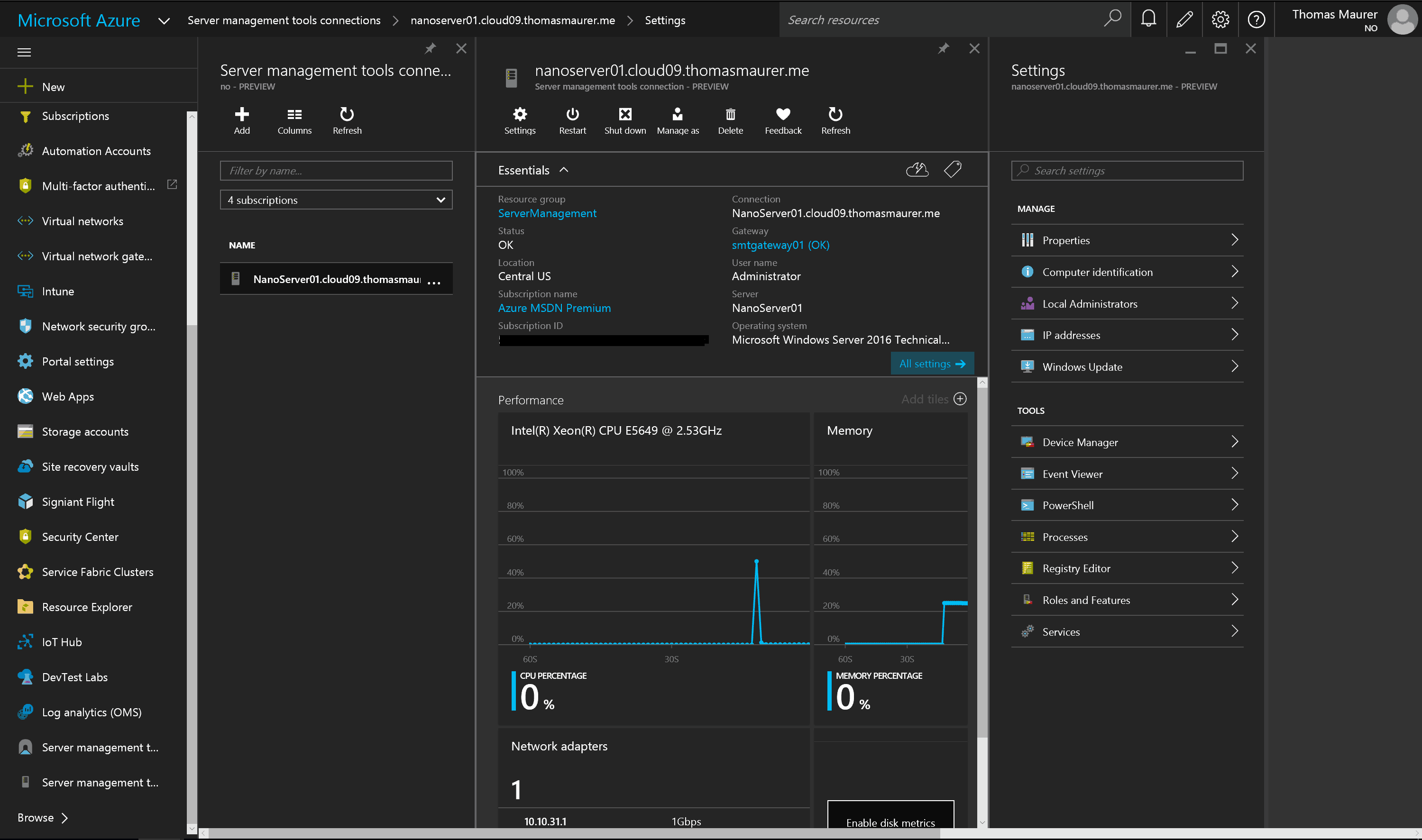
Manage Nano Server and Windows Server from Azure using Remote Server Management Tools
Today Microsoft announced the preview of the Remote Server Management Tools hosted in Azure, written by Kriti Jindal, a program manager on...
Summary: Update Rollup 8 for System Center 2012 R2 and Azure Pack now available
Yesterday Microsoft released Update Rollup 8 for System Center 2012 R2 and Windows Azure Pack....
List of Recommend Hotfixes and Updates for Hyper-V Network Virtualization (HNV)
I already made some post where I list the websites to recommended hotfixes and updates for Clusters, Hyper-V and File Server such as the...
Connect Microsoft Hyper-V Network Virtualization Gateway in System Center Virtual Machine Manager
If you are using Hyper-V Network Visualization you can use the Microsoft Hyper-V Network Virtualization Gateway for your Virtual Machines...