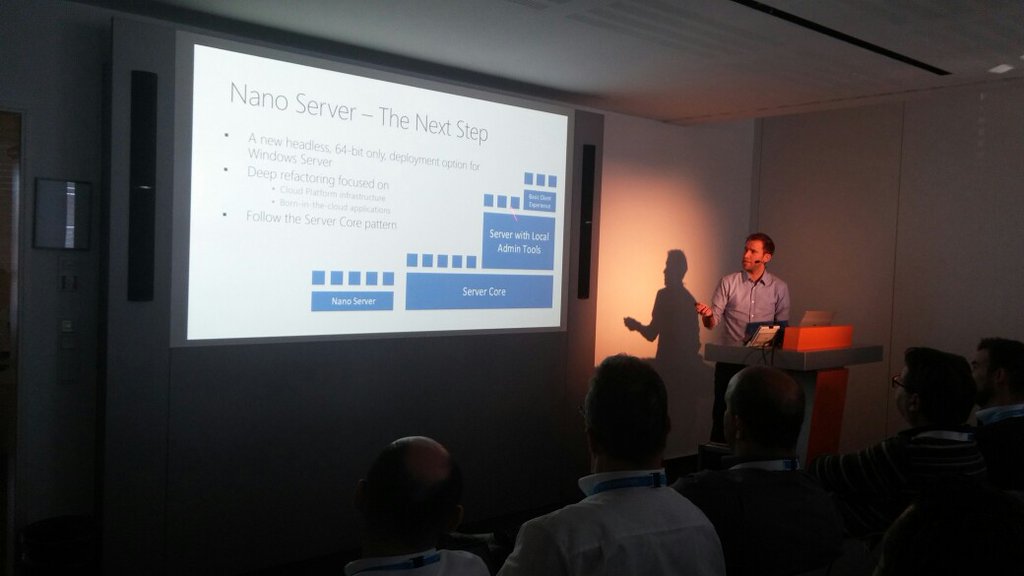
Nano Server – The future of Windows Server – Just enough OS
Finally, Microsoft released Windows Server 2016 and with Windows Server 2016 we also get the first...
Automated Active Directory Deployment with PowerShell
For a small presentation at KTSI I created a PowerShell script will automatically will deploys Active Directory Servers, adds other member...
Cisco UCS Hyper-V Cluster – Create Hyper-V Image for Blade Servers – Part 2
We use Microsoft Hyper-V Server 2008 R2 as Operating System for our Cisco Blade Notes. The Cisco...