Connect Ubiquiti UniFi Dream Machine to Azure VPN
A couple of days ago I got a Ubiquiti UniFi Dream Machine, which is an all-in-one device with an...
Create Azure P2S VPN with Azure AD authentication
A couple of days ago, we announced that you now can use Azure Active Directory to authentication Point-to-Site (P2S) VPN connections to...
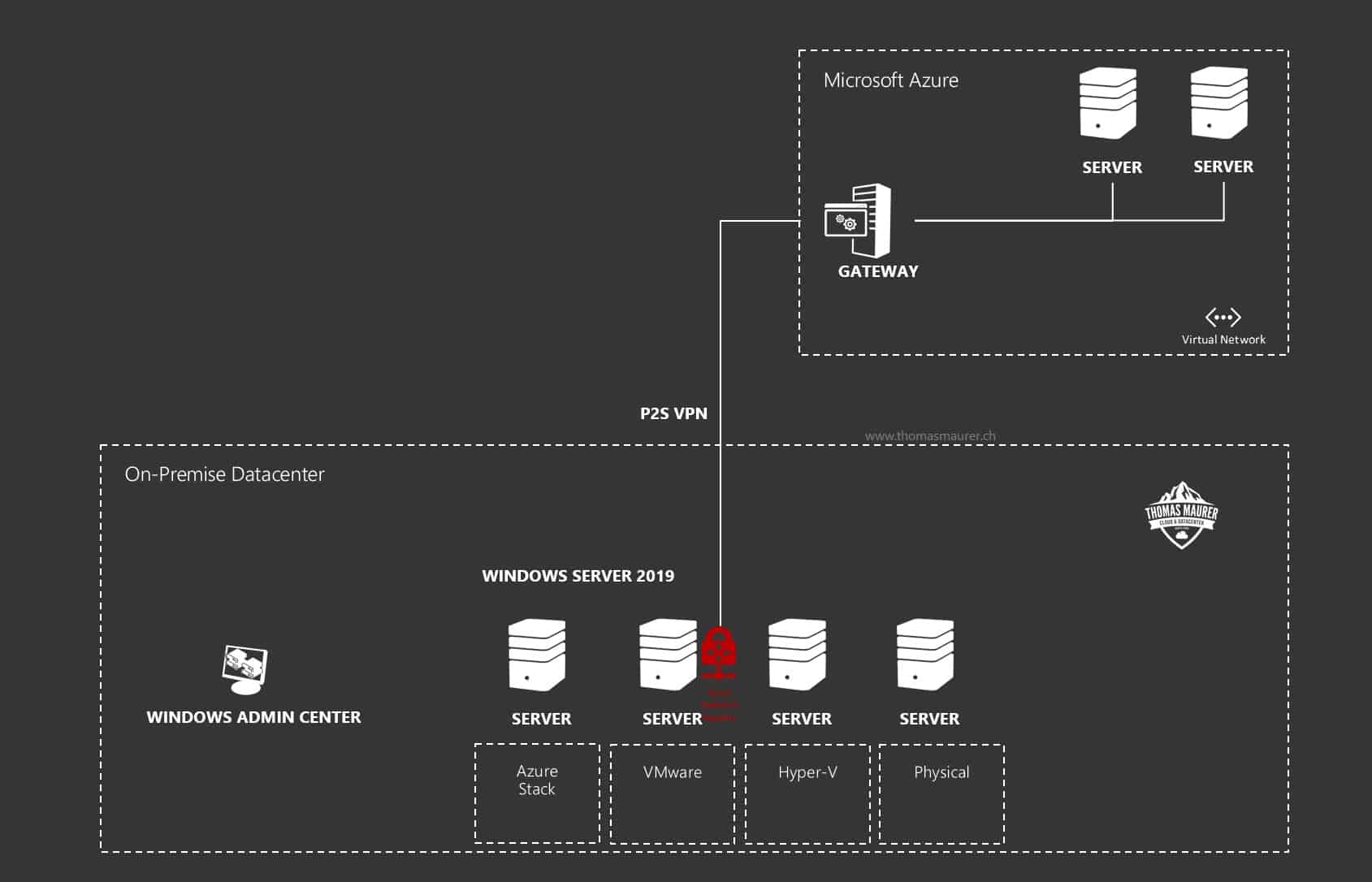
How to set up Windows Server Azure Network Adapter
In my series about Windows Server 2019, I have a new feature I want to introduce to you, called the Azure Network Adapter. The Azure...