Speaking at Deploy by ShareGate Online Event
I am happy to let you know that I will be speaking online at Deploy by ShareGate. Deploy is an...
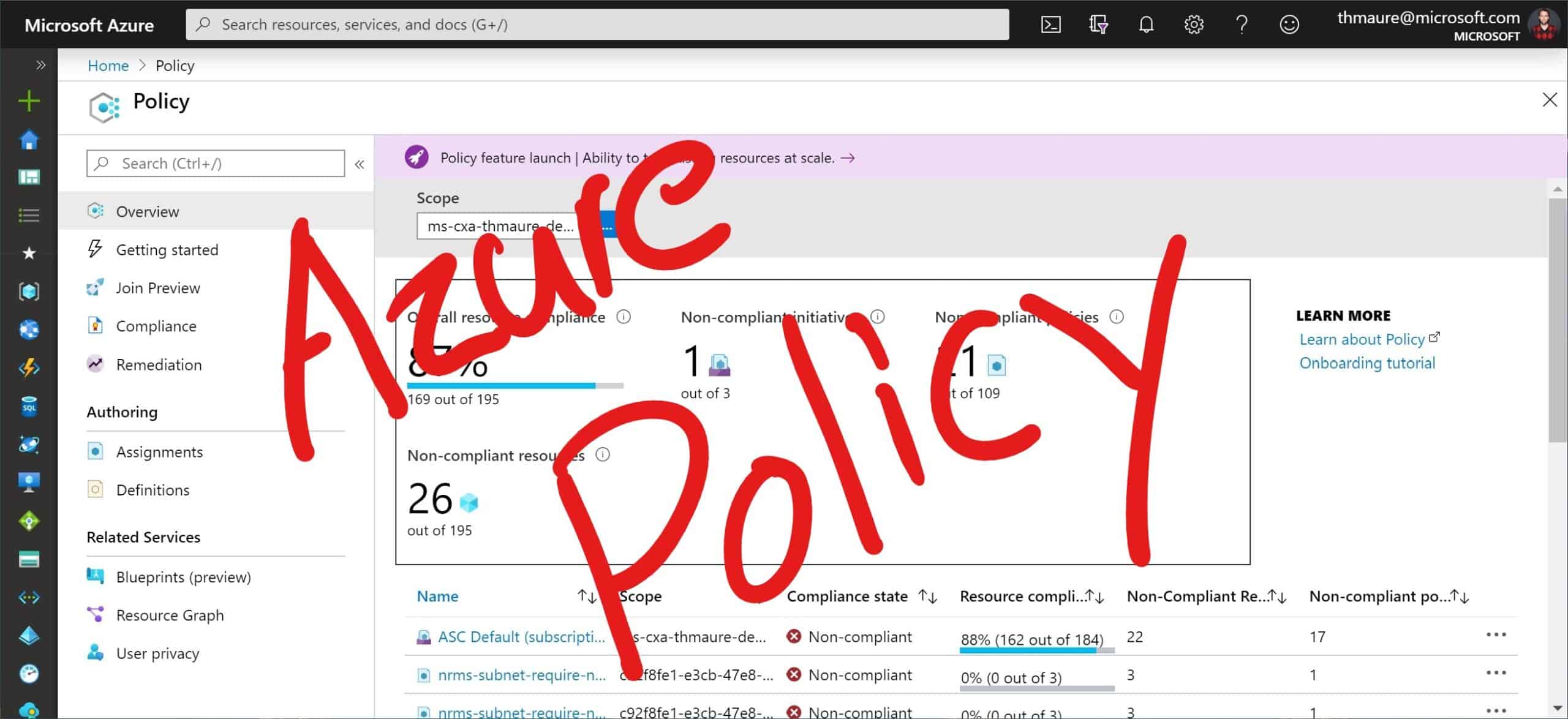
Keep control of your Azure environment with Azure Policy
Keeping control of your Azure environment and your Azure tenant can be challenging. Azure Policy is a fundamental part of Azure Governance...