As mentioned Azure Stack brings a true hybrid Cloud experience by bringing an consistent platform from the public cloud to the private cloud. There is a little bit of a catch, Microsoft Azure Stack of course only offers some of the Azure Public Cloud services, since for some of them you need to have a specific scale or specialized hardware, and they often they are behind in feature and functionality, since Azure gets updated daily and Azure Stack gets a slower updated cycle.
But what if you want to develop services on Azure, which should be compatible with Azure Stack, how can you make sure that these services also work on Azure Stack? The anwser to that is the Azure Stack Policy Module. The Azure Stack Policy module allows you to configure an Azure subscription with the same versioning and service availability as Azure Stack using Azure Policy. The module uses the New-AzureRMPolicyAssignment PowerShell cmdlet to create an Azure policy, which limits the resource types and services available in a subscription. You can then use your Azure subscription to develop apps targeted for Azure Stack.
You can find the Azure Stack Policy Module in Azure Stack tools on GitHub.
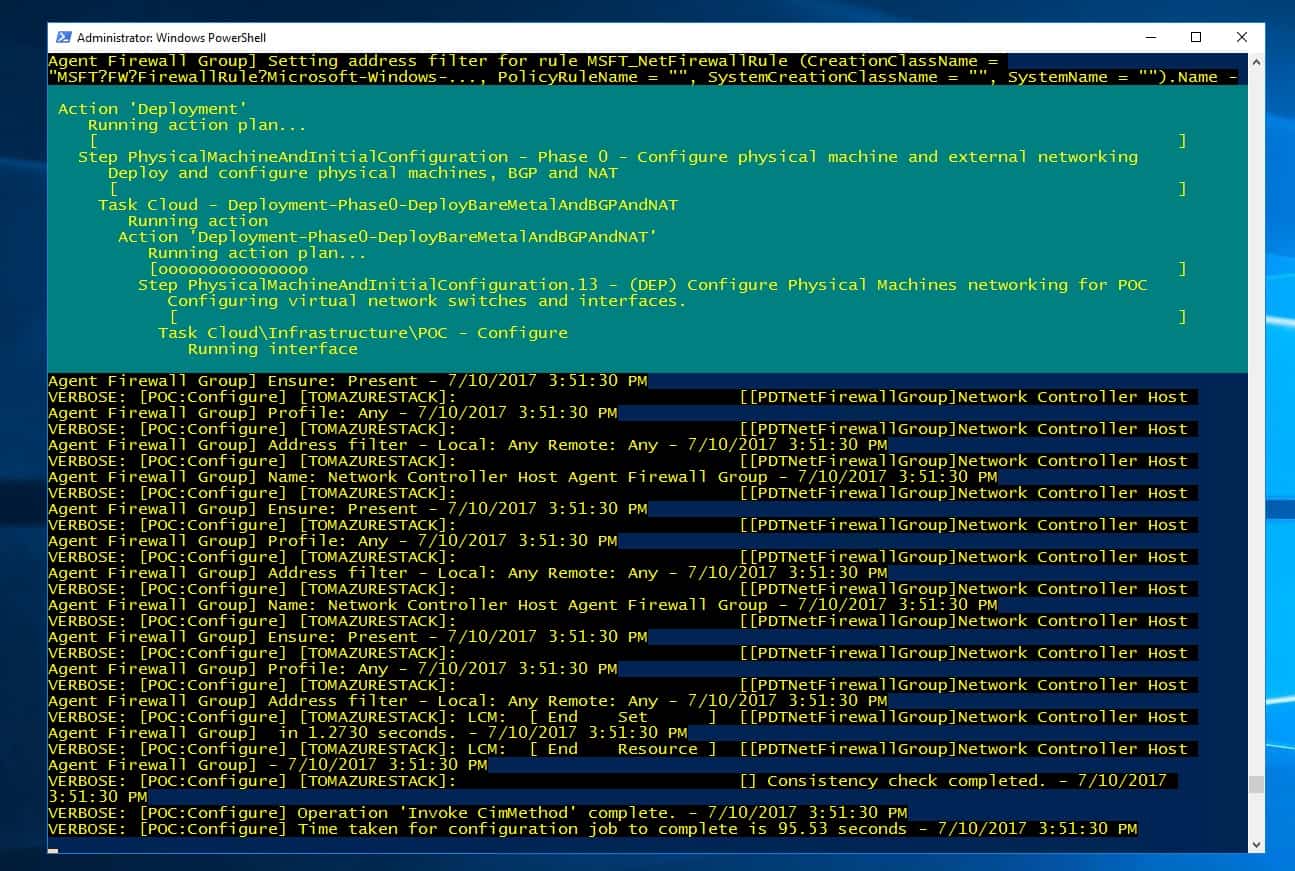
Install the Azure Stack Policy Module
- Install the required version of the AzureRM PowerShell module, as described in Step1 of Install PowerShell for Azure Stack.
- Download the Azure Stack tools from GitHub
- Configure PowerShell for use with Azure Stack
- Import the AzureStack.Policy.psm1 module:
Import-Module .\Policy\AzureStack.Policy.psm1
Apply policy to subscription
The following command can be used to apply a default Azure Stack policy against your Azure subscription.
Login-AzureRmAccount $s = Select-AzureRmSubscription -SubscriptionName "<Azure Subscription Name>" $policy = New-AzureRmPolicyDefinition -Name AzureStackPolicyDefinition -Policy (Get-AzsPolicy) $subscriptionID = $s.Subscription.SubscriptionId New-AzureRmPolicyAssignment -Name AzureStack -PolicyDefinition $policy -Scope /subscriptions/$subscriptionID
Apply policy to a resource group
You may want to apply policies in a more granular method. As an example, you may have other resources running in the same subscription. You can scope the policy application to a specific resource group, which lets you test your apps for Azure Stack using Azure resources.
Login-AzureRmAccount $rgName = 'myRG01' $s = Select-AzureRmSubscription -SubscriptionName "<Azure Subscription Name>" $policy = New-AzureRmPolicyDefinition -Name AzureStackPolicyDefinition -Policy (Get-AzsPolicy) New-AzureRmPolicyAssignment -Name AzureStack -PolicyDefinition $policy -Scope /subscriptions/$subscriptionID/resourceGroups/$rgName
You can find more information about this on the official documentation page: https://docs.microsoft.com/en-us/azure/azure-stack/user/azure-stack-policy-module
Tags: Azure, Azure Policy, Azure Stack, Azure Stack Policy Module, Microsoft, Microsoft Azure, PowerShell Last modified: August 18, 2018